| Cryptography |
| |
| Symmetric-Key Cryptography |
| |
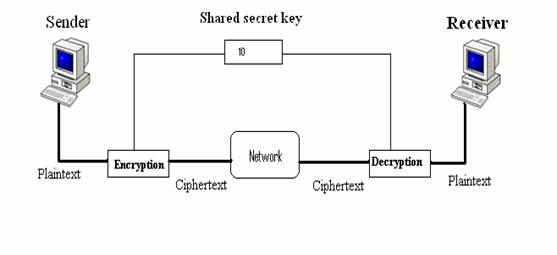
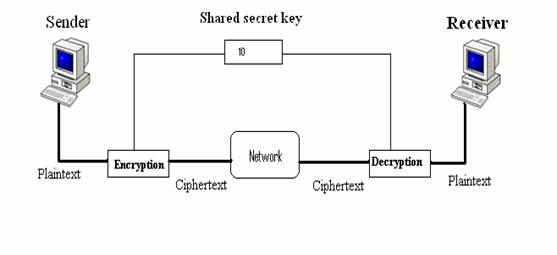
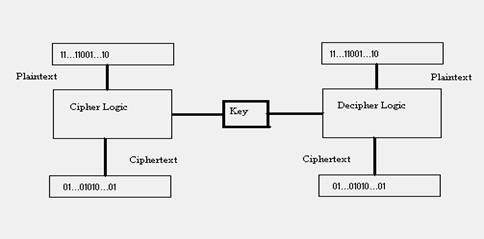
| In symmetric-key cryptography, the same key is used by both parties. |
| |
| The sender uses this key and an encryption algorithm to encrypt data; the receiver uses the same key and the corresponding decryption algorithm to decrypt the data |
| |
 |
| |
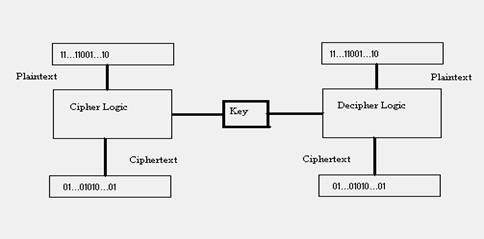
| In symmetric-key cryptography, the algorithm used for decryption is the inverse of the algorithm used for encryption. |
| |
| This means that if the encryption algorithm uses a combination of addition and multiplication, the decryption algorithm uses a combination of division and subtraction. |
| |
| Traditional Ciphers |
| |
| In the earliest and simplest ciphers, a character was the unit of data to be encrypted. These traditional ciphers involved either substitution or transposition. |
| |
| Substitution Cipher |
| |
| A cipher using the substitution method substitutes one symbol with another. If the symbols in the plaintext are alphabetic characters, we replace one character with another. |
| |
| For example, we can replace character A with D and character T with Z. If the symbols are digits (0 to 9), we can replace 3 with 7 and 2 with 6. |
| |
| We will concentrate on alphabetic characters. Substitution can be categorized as either monoalphabetic or polyalphabetic. |
| |
| Monoalphabetic Substitution |
| |
| In mono alphabetic substitution, a character in the plaintext is always changed to the same character in the ciphertext regardless of its position in the text. |
| |
| For example, if the algorithm says that character A in the plaintext must be changed to character D, every character A is changed to character D, regardless of its position in the text. |
| |
| The first recorded ciphertext was used by Julius Caesar and is still called the Caesar cipher. |
| |
| Example |
| |
| ATTACK becomes |
| |
| DWWDFN |
| |
| Polyalphabetic Substitution |
| |
| In polyalphabetic substitution, each occurrence of a character can have a different substitute. The relationship between a character in the plaintext to a character in the ciphertext is one-to-many. |
| |
| Character A can be changed to D in the beginning of the text, but it could be changed to N at the middle. We discuss a very simple one. |
| |
| It is obvious that if the relationship between plaintext characters and ciphertext characters is one-to-many, the key must tell us which of the many possible characters can be chosen for encryption. |
| |
| Let us define our key as "take the position of the character in the text, divide the number by 9, and let the remainder be the shift value." |
| |
| With this scenario, the character at position 1 will be shifted one character, the character at position 2 will be shifted two characters, and the character in position 14 will be shifted four characters (14 mod 9 is 4).So now the word ATTACK becomes |
| |
| A T T A C K -plaintext |
| |
| B V W E H Q -encrypted |
| |
| Transpositional Cipher |
| |
| In a transpositional cipher, the characters retain their plaintext form but change their positions to create the ciphertext. |
| |
| The text is organized into a two-dimensional table, and the columns are interchanged according to a key. The key defines which columns should be swapped. |
| |
| As you have guessed, transpositional cryptography is not very secure either. |
| |
| The character frequencies are preserved, and the attacker can find the plaintext through trial and error. |
| |
| This method can be combined with other methods to provide more sophisticated ciphers. |
| |
| Example |
| |
| 7 4 5 1 2 9 3 6 KEY |
| |
| P L E A S E T R |
| |
| A N S F E R O N |
| |
| E M I L L I O N |
| |
| D O L L A R S T plain text |
| |
| O M Y S W I S S |
| |
| B A N K A C C O |
| |
| U N T S I X T W |
| |
| O T W O A B C D |
| |
| Plaintext |
| |
| PLEASE TRANSFER ONE MILLION DOLLARS IN MY SWISS BANK ACCOUNT SIX TWO TWO. |
| |
| Ciphertext |
| |
| AFLLSKSOSELAWAIATOOSSCTCLNMOMANTESILYNTWRNNTSOWDPAEDOBUOERIRICXB |
| |
| Block Cipher |
| |
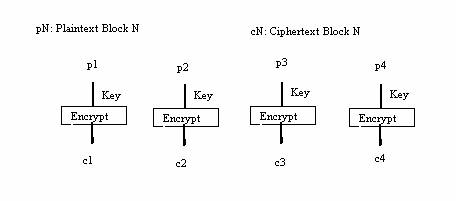
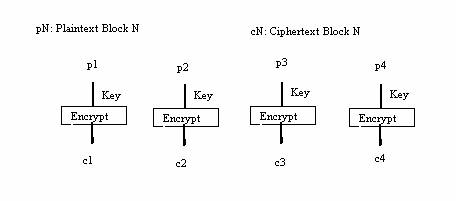
| Traditional ciphers used a character or symbol as the unit of encryption/decryption. Modem ciphers, on the other hand, use a block of bits as the unit of encryption/decryption. |
| |
| Figure shows the concept of the block cipher; the plaintext and ciphertext are blocks of bits. |
| |
 |
| |
| Operation Modes |
| |
| Ciphers that operate on eight-character segments are too short now the question arises, Can we encrypt and decrypt longer messages (900 characters, e.g.)? |
| |
| Several modes have been defined, and we briefly describe the most common one. |
| |
| Electronic Code Block (ECB) Mode |
| |
| In electronic code block (ECB) mode, we divide the long message into 64-bit blocks and encrypt each block separately, as shown in Figure. |
| |
 |
| |
| |
| |
| |
| |